Security+ SY0-601 Prep
محتوى الدورة
الدروس [مكتملة]
-
40:49
-
37:49
-
02- Explaining Threat Actors and Threat Intelligence
57:45 -
03.1- Performing Security Assessments – Part 1
55:31 -
03.2- Performing Security Assessments – Part 2 (Exploring the Lab Environment Lab)
29:15 -
03.3- Performing Security Assessments – Part 3 (Scanning and Identifying Network Nodes Lab)
32:15 -
03.4- Performing Security Assessments – Part 4
33:51 -
03.5- Performing Security Assessments – Part 5 (Intercepting and Interpreting Network Traffic with Packet Sniffing Tools Lab)
30:54 -
03.6- Performing Security Assessments – Part 6
59:55 -
03.7- Performing Security Assessments – Part 7 (Analyzing the Results of a Credentialed Vulnerability Scan Lab)
25:50 -
04.1- Identifying Social Engineering and Malware – Part 1
46:39 -
04.2- Identifying Social Engineering and Malware – Part 2
55:01 -
04.3- Identifying Social Engineering and Malware – Part 3 (Installing, Using, and Blocking a Malware-based Backdoor Lab)
27:26 -
05- Summarizing Basic Cryptographic Concepts
01:40:21 -
06.1- Implementing Public Key Infrastructure – Part 1
01:02:48 -
06.2- Implementing Public Key Infrastructure – Part 2 (Managing the Lifecycle of a Certificate Lab)
32:50 -
07.1- Implementing Authentication Controls – Part 1
01:21:33 -
07.2- Implementing Authentication Controls – Part 2 (Auditing Passwords with a Password Cracking Utility Lab)
35:47 -
07.3- Implementing Authentication Controls – Part 3 (Managing Centralized Authentication Lab)
30:11 -
08.1- Implementing Identity and Account Management Controls – Part 1
01:18:15 -
08.2- Implementing Identity and Account Management Controls – Part 2 (Managing Access Controls in Windows Server Lab)
33:57 -
08.3- Implementing Identity and Account Management Controls – Part 3 (Configuring a System for Auditing Policies Lab)
33:28 -
08.4- Implementing Identity and Account Management Controls – Part 4 (Managing Access Controls in Linux Lab)
35:39 -
09.1- Implementing Secure Network Designs – Part 1
57:40 -
09.2- Implementing Secure Network Designs – Part 2
01:20:11 -
09.3- Implementing Secure Network Designs – Part 3 (Implementing a Secure Network Design Lab)
32:02 -
10.1- Implementing Network Security Appliances – Part 1
01:06:16 -
10.2- Implementing Network Security Appliances – Part 2 (Configuring a Firewall Lab)
22:32 -
10.3- Implementing Network Security Appliances – Part 3 (Configuring an Intrusion Detection System Lab)
35:10 -
11.1- Implementing Secure Network Protocols – Part 1
01:04:30 -
11.2- Implementing Secure Network Protocols – Part 2 (Implementing Secure Network Addressing Services Lab)
25:46 -
11.3- Implementing Secure Network Protocols – Part 3 (Implementing a Virtual Private Network Lab)
21:20 -
11.4- Implementing Secure Network Protocols – Part 4 (Implementing a Secure SSH Server Lab)
41:08 -
12.1- Implementing Host Security Solutions – Part 1
17:24 -
12.2- Implementing Host Security Solutions – Part 2 (Implementing Endpoint Protection Lab)
22:14 -
13- Implementing Secure Mobile Solutions
25:14 -
14.1- Summarizing Secure Application Concepts – Part 1
55:10 -
14.2- Summarizing Secure Application Concepts – Part 2 (Identifying Application Attack Indicators Lab)
29:29 -
14.3- Summarizing Secure Application Concepts – Part 3 (Identifying a Browser Attack Lab)
34:52 -
14.4- Summarizing Secure Application Concepts – Part 4 (Implementing PowerShell Security Lab)
33:59 -
14.5- Summarizing Secure Application Concepts – Part 5 (Identifying Malicious Code Lab)
24:35 -
15- Implementing Secure Cloud Solutions
49:26 -
16- Explaining Data Privacy and Protection Concepts
24:15 -
17.1- Performing Incident Response – Part 1
59:59 -
17.2- Performing Incident Response – Part 2 (Managing Data Sources for Incident Response Lab)
41:56 -
17.3- Performing Incident Response – Part 3 (Configuring Mitigation Controls Lab)
18:33 -
18.1- Explaining Digital Forensics – Part 1
11:42 -
18.2- Explaining Digital Forensics – Part 2 (Acquiring Digital Forensics Evidence Lab)
34:19 -
19- Summarizing Risk Management Concepts
44:00 -
20.1- Implementing Cybersecurity Resilience – Part 1
11:07 -
20.2- Implementing Cybersecurity Resilience – Part 2
23:42 -
21- Explaining Physical Security
16:36 -
All Slides
00:00 -
All Videos
00:00 -
Full Course on Youtube
00:00
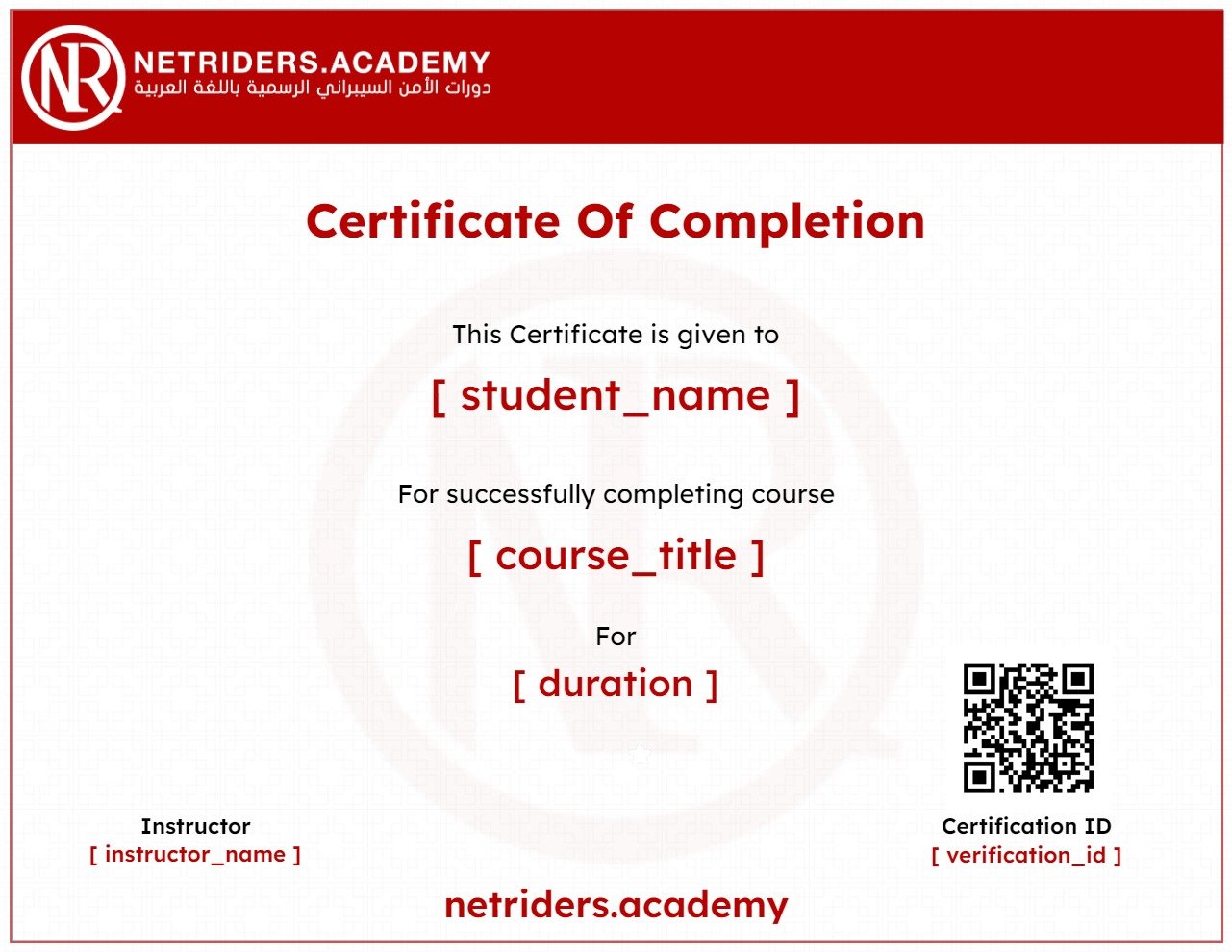
احصل على شهادة اتمام الدورة بعد الإنتهاء
أضف هذه الشهادة إلى سيرتك الذاتية لإثبات مهاراتك وزيادة فرصك في الحصول علي وظيفة.
تقييمات ومراجعات الطلاب
very good
NICE
ما شاء الله م احمد شخص محترم جدا و ممتاز فعلا مبيفوتش معلومة ربنا يباركله و يجزيه كل خير
من افضل الكورسات اللي تخلي الواحد يفتح عقله على السيكيوريتي و مدخل قوي جدا ليها
شرح جميل وفيه كل التفاصيل المهمة.
was really great explanation for Mr.Ahmed but i would prefer some actual labs not just videos from labs
good
تم تطوير معلوماتي بالفعل و كان مناسبا جدا
جميلة فتحت نظري على مجالات عديده

